This year, HashiCorp’s European user conference evolved into something a bit different. Last year, HashiConf Europe was a two-day event in Amsterdam; this year, HashiDays was a single-day event taking place in London, Paris, and Munich at the same time.

An eventful journey to London
My employer, AT Computing, is a HashiCorp partner, and I was lucky enough to attend HashiDays London as a HashiCorp Ambassador. Together with three colleagues, I traveled by train from the Netherlands to London on Monday June 12, the day before the event. That meant a long day of traveling for me, and due to delays on the track, we barely made our connection in Brussels — we were the last people to be expedited through customs.
We arrived at St. Pancras in London at 4 p.m. and took the Underground to our hotel. Turns out it helps if you take the subway in the right direction, so we didn’t make it there until after 5 p.m. After checking in, we headed straight to the nearest pub.

Later in the evening there was a get-together with the other Ambassadors. HashiCorp CTO and Co-Founder Armon Dadgar also joined us at one point.
Starting HashiDays early
On Tuesday we got up early and took the Underground to the HashiDays venue, Events @ No 6 in Aldgate. Upon arrival we picked up our badges and swag packs. After shaking hands with some familiar faces, we joined the rest of the visitors enjoying the well-prepared breakfast. The venue filled quickly before the doors of the room opened and we took our seats.

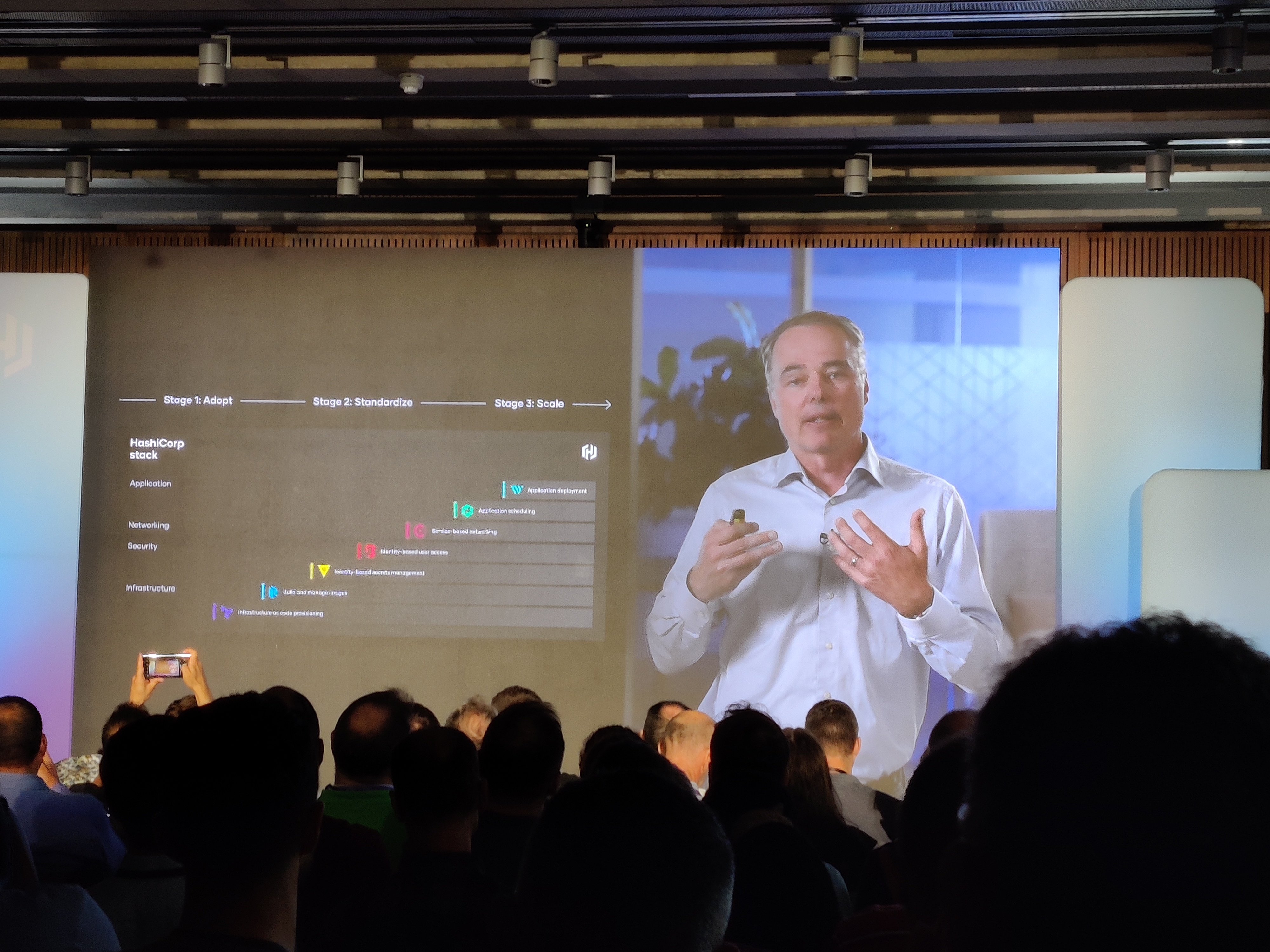
After a short introduction from MC Rob Barnes, HashiCorp Senior Developer Advocate, the floor was handed over to a virtual Dave McJannet, the HashiCorp CEO, to start the keynote. Attendees at HashiDays Munich got a live presentation from Dave, who was in attendance there.
In his segment, he shared the results of the 2023 HashiCorp State of Cloud Strategy Survey, and one thing that stood out to me is that the most common barrier for moving to the cloud is a shortage of the needed skills.
It seems that the world of IT drives forward as if the skills gap is not real or relevant. In that regard, as a leader of the HashiCorp User Group (HUG) in Amsterdam, I was pleasantly surprised to learn that there are now more than 165 HUGs operating around the world.
After Dave’s introduction, Armon took the stage in London to continue the keynote by zooming in on the new features being announced for HashiCorp Terraform, Vault, Boundary, and Consul.

New features for HashiCorp Terraform, Vault, Boundary, and Consul.
First up was Vault and the launch of a public beta for HCP Vault Secrets, which I knew about as part of the Early Adopter Program. HCP Vault Secrets is a SaaS solution that simplifies the core Vault experience to focus on making it easy to centralize static secrets. Just like Vault, HCP Vault Secrets can be accessed via GUI, CLI, and API and can also be integrated into Terraform. There is also the ability to sync secrets with other sources: Think of a GitHub or a multi-cloud AWS Secrets Manager to ensure that all these secrets end up being managed in Vault.
Next up was the GA release of the Vault Secrets Operator for Kubernetes, where the various Vault Agent sidecars — previously required — are made redundant as Vault talks to Kubernetes at a higher layer. It’s an elegant solution in which the application within Kubernetes no longer needs to be Vault-aware; the application can just use Kubernetes secrets created and managed by Vault.
In the Boundary announcements we learned about the new self-managed Boundary Enterprise edition, and the new SSH session recording feature. Session recording makes it possible to monitor certain Boundary SSH targets and to record their sessions so that a Boundary administrator can conduct forensic investigations on the relevant sessions in the event of a (security) issue. All this is stored in an Amazon S3 bucket, at least for now.
Next it was Consul's turn: a central management plane, or dashboard, is now available within HCP Consul that covers all your Consul clusters, including HCP Consul or self-managed Consul clusters. It’s very nice to have all the data at hand for trends and initial troubleshooting. Another new addition was the GA release of cluster peering, which enables you to peer Consul clusters in a simple way. This used to be a rather complicated process; fine for a small environment with a few clusters, but more and more complicated as the number of clusters grew.
Another new feature is the Link Self-Managed Cluster option, which was released in beta. You can now link existing self-managed Consul clusters to the new management plane in HCP Consul. The public beta of the observability module, meanwhile, gives you even more insight into the metrics of your service mesh and also Envoy telemetry data between services.
In addition to these big announcements, a number of separate (beta) updates are on tap for Consul 1.16 (beta), including “sameness groups” and FIPS 140-2 compliance for Consul Enterprise.
Last, but certainly not least, we got a review of recent Terraform feature updates, including projects, variable sets, and dynamic provider credentials. Attention was paid to Vault-backed dynamic credentials and no-code provisioning: a way to offer Terraform modules in a graphical interface with the help of input fields so end users don’t need to know anything about Terraform and can deploy infrastructure without code.
That set the stage for the introduction of new Terraform features. The new explorer feature in Terraform Cloud, for example, increases the observability of your workspaces, making it easy to see the state of Terraform versions and associated modules in your landscape.
Then HashiCorp fulfilled the long-held wish of many engineers: shifting the import method from a manual and somewhat cumbersome import function to a config-driven import function. Without affecting your Terraform state, you can now instantly import one or more resources, and Terraform generates the code for you and saves it as a separate .tf file. These resource blocks are defined with all settings from the resource being imported. This saves so much work and it’s also a lot safer because these changes take place only after a Terraform apply and then are active only in the state. This way you can check in advance whether there are unintentional changes to your infrastructure due to the import.
Breakout sessions, lunch, and more breakout sessions

The room was packed, and in between the sessions we were guided by MC Rob. After a short break, we attended two breakout sessions about Terraform and HCP Vault Secrets, which re-arranged the product updates and added clarifications of the new features.
Then it was time for lunch and a group photo with all the Ambassadors we could round up. After that it was time for the next sessions, focusing on how to use Terraform to safely gain traction on the migration to the cloud.
The last sessions of the day were Learn Labs, where we participated in various scenarios led by an on-stage instructor. The first session addressed HCP Boundary and how to inject SSH credentials with a private Vault cluster. Coincidentally, I had previously created my own presentation on how to achieve this, and it was very valuable to see the difference in approach between mine and the one presented by HashiCorp. The closing session covered how you can use dynamic provider credentials with Terraform.

That marked the end of the official program, and attendees headed to the roof terrace for a barbecue. This gave us time to mingle and network without worrying about when the next session would start. We found a quiet spot and enjoyed our meal, the view, and the sunshine.

After leaving the venue, we cooled off at the appropriately named Tower Bridge Vault Bar, where we discussed the day’s sessions over a drink. We walked a scenic route through London back to our hotel. We left early the next morning and arrived home around 4 p.m. local time.
The skills gap is real

When I think about everything we experienced at HashiDays London, apart from the new product features, what stuck with me the most is that the number 1 barrier to multi-cloud success is a skills gap that prevents projects from getting started and keeps people from being comfortable in their current roles. Working for a company that has been providing UNIX/Linux and open source training for almost 40 years, it’s nice to know that we work to reduce this skill gap on a daily basis.
Now I can’t wait for HashiConf Global in San Francisco, October 10-12, and more news about HashiCorp’s products.
from HashiCorp Blog https://bit.ly/3pmNOiI
via IFTTT
No comments:
Post a Comment