The Good | Developer Uncovers Backdoor Planted in XZ Utils
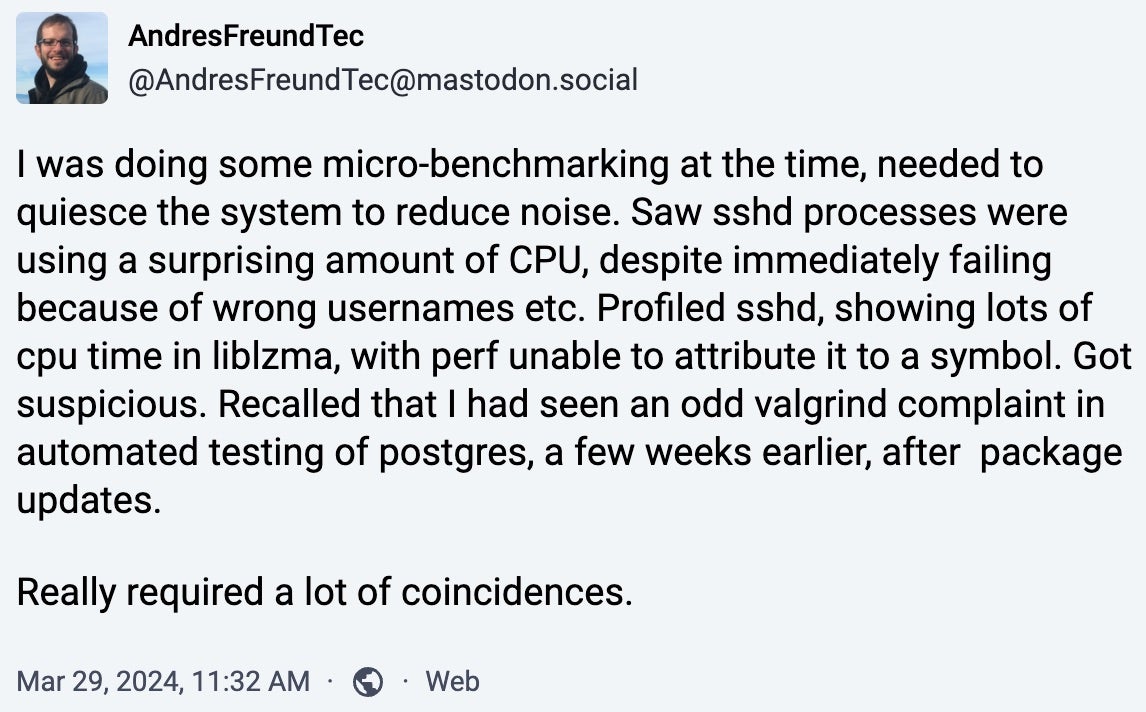
Over the Easter weekend, software developer Andres Freund uncovered a backdoor hidden within XZ Utils, an open-source data compressor ubiquitous in nearly all Linux-based systems. Currently, the supply chain flaw is tracked as CVE-2024-3094 (CVSS score: 10.0) and is being described as what could have been a highly sophisticated outbreak rivaling even that of the SolarWinds supply chain attack of 2020.
The backdoor was likely a multi-year-long effort, intentionally planted by an XZ Utils project maintainer named Jia Tan (aka Jia Cheong Tan or JiaT75). Tan allegedly worked his way up to this role over the span of two years to establish legitimacy in his role before introducing a series of changes to the software in 2023.
The changes were eventually included in the data compressor’s February 2024 release, affecting XZ Utils versions 5.6.0 and 5.6.1. The backdoor made it to some Linux releases including Debian Unstable, Fedora Linux 40, Kali Linux, and Fedora Rawhide, which have all since been rolled back.
The backdoor targets sshd, the executable file responsible for remote SSH connections. With a specific encryption key, a threat actor could have embedded any code within an SSH login certificate, enabling them to upload and execute it on affected devices. Although no actual code uploads have been observed, the potential risks would have included theft of encryption keys or malware deployment.
Freund’s stroke of luck diverted the potential of a very serious supply chain attack, but the event is a sharp reminder to prioritize security in OSS maintenance. Since the discovery of the XZ Utils compromise, other open source software maintainers have commented on the problem of bullying in OSS projects and raised concerns that the XZ story may not be an isolated incident.
Regular audits, thorough code reviews, and prompt patching are essential to addressing threats effectively.
The Bad | Missouri County Declares State of Emergency After Ransomware Attack
Home to over 717,000 residents, one of the largest counties in Missouri was hit this week with a confirmed ransomware attack, disrupting several critical services. In the wake of the attack, Jackson County offices responsible for tax payment, marriage licensing, and inmate management systems have all shut down until further notice while investigations continue.
Jackson County Offices Closed Wednesday, April 3
Jackson County offices will be closed April 3rd as we work through updating our system from the ransomware attack. Check back tomorrow for more information on opening and closures of county offices. https://t.co/e5uVfwakhI pic.twitter.com/kwatK3nAg8
— Jackson County MO (@JacksonCountyMO) April 3, 2024
So far, law enforcement agencies, including the FBI and the Department of Homeland Security, have been notified, and external IT security experts are assisting in the ongoing incident response. The County Executive has also issued a state of emergency to expedite IT measures and service restoration.
County officials have also assured residents that the compromised systems did not store financial data – specifically, information handled by the Payit payment service provider, which is independently managed outside the county’s network. The county collaborates with Payit to provide secure resident engagement and payment services for property taxes, marriage licenses, and more.
The shutdowns happened on the same day as a special election held by the county to decide on a proposed sales tax aimed at financing a new stadium for the Kansas City MLB and NFL teams. Officials have emphasized that both the Jackson County Board of Elections and the Kansas City Board of Elections remain unaffected by the cyberattack, with no indication of data compromise and both boards continuing their normal operations.
The attack on the Missouri county is now the 18th of ransomware incidents on state and local governments since the start of 2024. Researchers note that government entities will continue to be targeted by transnational threat groups – a reality triggered by aging IT infrastructures of underfunded agencies as well as a widening gap in skilled cybersecurity professionals working in government.
The Ugly | DinodasRAT Backdoor Targets Linux Servers Across Eastern Hemisphere
New findings emerged this week of a Linux variant for DinodasRAT (aka XDealer), a multi-platform backdoor attributed to a number of China-linked APTs. Reporting on the latest series of attacks, security researchers note the new variant to be targeting entities in China, Taiwan, Turkey, and Uzbekistan.
The Linux version primarily targets Red Hat and Ubuntu systems. It establishes persistence using SystemV or SystemD startup scripts and communicates with remote servers for commands over TCP or UDP. Capabilities include file operations, process enumeration, shell command execution, and evasion techniques against detection tools.
An initial Linux variant (V10) was first spotted in early October 2023, with evidence tracing back to a previous version (V7) from July 2021.
DinodasRAT aims to gain and maintain control over infected machines with the main goals of data exfiltration and espionage. The backdoor creates a distinct identification code for every compromised device by combining the infection date, hardware details, and backdoor version. This code is then saved in a concealed configuration file, aiding in the monitoring and control of compromised systems. To operate covertly and avoid discovery, DinodasRAT alters file access timestamps, reducing its traceability and complicating efforts for security experts to identify and counter the threat.
The remote access trojan has cropped up in various threat campaigns over the past half year. In October 2023, attackers used DinodasRAT to spy on the Guyanese government. Just earlier this month, the trojan was seen again in the hands of Chinese APT group, Earth Krahang, to compromise both Linux and Windows systems of governments worldwide.
This string of attacks illustrate the maturing of China’s cyber espionage ecosystem, meaning sectors will need to continuously factor in geopolitical risks and focus their cyber strategy on building resilience.
from SentinelOne https://ift.tt/ftoNYSg
via IFTTT
No comments:
Post a Comment