The Good | Global Authorities Disrupt Tycoon2FA, LeakBase & Phobos Ransomware
Europol has successfully disrupted Tycoon2FA in an international operation, taking down the phishing-as-a-service (PhaaS) platform responsible for sending tens of millions of phishing emails each month. Authorities seized 330 domains used to host phishing pages and control infrastructure.
Active since 2023, Tycoon2FA enabled attackers to bypass multi-factor authentication (MFA) using adversary-in-the-middle (AitM) techniques that captured credentials and session cookies. Sold through Telegram for about $120, the service allowed low-skill criminals to launch large-scale phishing attacks against organizations worldwide.
In another seizure, LeakBase, a major cybercrime forum used to trade stolen data and hacking tools, was taken down as part of Operation Leak, a joint effort by the FBI, Europol, and law enforcement in 14 countries. Police seized two domains, posted seizure banners, executed search warrants, and made arrests worldwide.
LeakBase had amassed 142,000 members since 2021 and offered leaked databases, exploits, and cybercrime services. All forum data, including accounts, messages, and IP logs, have been preserved for evidence, with the seizure now entering a prevention phase to deter further cybercrime.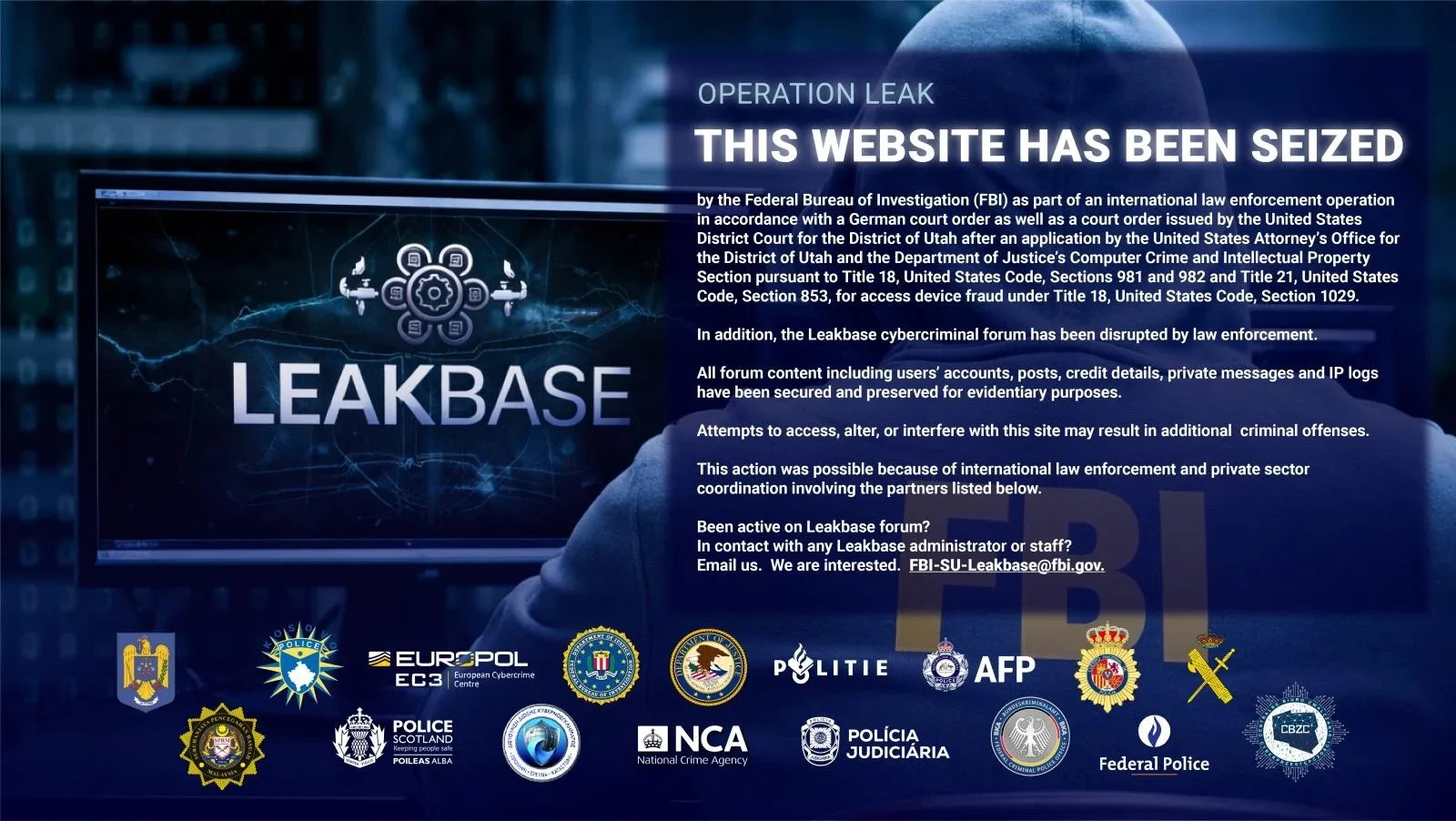
A Russian national, Evgenii Ptitsyn, has pleaded guilty to wire fraud conspiracy for his role running the Phobos ransomware operation. Since 2020, Phobos has targeted over 1000 organizations worldwide, including schools, hospitals, and government agencies, collecting more than $39 million in ransom payments. Phobos affiliates were responsible for infiltrating victim networks, encrypting data, exfiltrating sensitive files, and paying Ptitsyn a per-deployment fee in exchange for the corresponding decryption keys.
Ptitsyn himself managed ransomware sales, distributed decryption keys, and took a cut of all affiliate payments. His sentencing is scheduled for July 15, facing up to 20 years.
The Bad | Researchers Uncover ‘Coruna’ Exploit Kit Mass Targeting iOS Devices
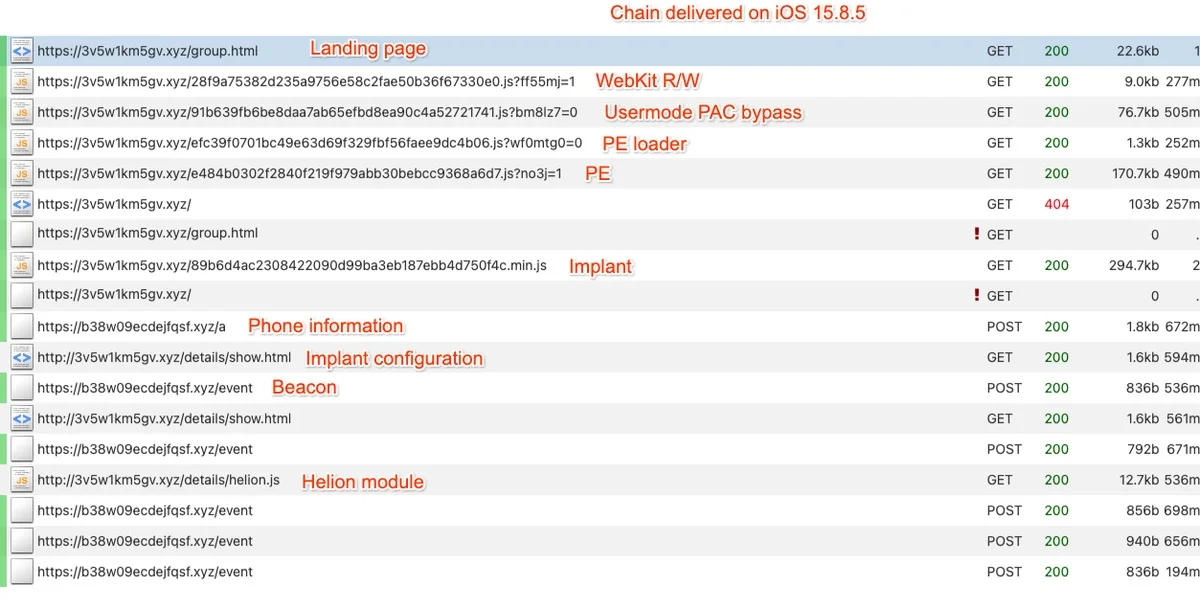
Multiple threat actors have deployed Coruna, a previously unknown iOS exploit kit containing 23 exploits and five complete exploit chains capable of targeting Apple devices running iOS 13 through iOS 17.2.1.
Researchers first observed parts of the Coruna framework in February 2025 while investigating activity linked to a commercial surveillance vendor. The exploit kit uses a sophisticated JavaScript delivery framework that fingerprints a victim’s device and operating system before selecting the most effective exploit chain.
Several of the exploits rely on advanced techniques such as WebKit remote code execution (RCE), pointer authentication code (PAC) bypasses, sandbox escapes, kernel privilege escalation, and Page Protection Layer (PPL) bypasses. Some vulnerabilities included in the kit were previously associated with Operation Triangulation, a high-profile iOS espionage campaign uncovered in June 2023.
Over time, Coruna has spread across different threat ecosystems. In mid-2025, a suspected Russian espionage group UNC6353 used the framework in watering hole attacks targeting visitors to compromised Ukrainian websites. Later that year, the exploit kit appeared on fake Chinese cryptocurrency and gambling websites linked to a financially-motivated threat actor.
Once exploitation succeeds, attackers deploy a loader known as PlasmaLoader, which downloads additional modules designed primarily to steal cryptocurrency wallet data and sensitive information. Targeted data includes wallet recovery phrases, financial information, and other stored text. Stolen data is encrypted before being transmitted to attacker-controlled infrastructure.
Coruna demonstrates how advanced spyware-grade exploit frameworks can spread from surveillance vendors to nation-state actors and eventually cybercriminal groups, highlighting the growing commercialization and reuse of sophisticated zero-day capabilities in the mobile threat landscape.
The Ugly | Hacktivists Launch Retaliatory Cyberattacks After U.S.–Israel Strikes on Iran
Following the U.S.-Israel military operations against Iran, cybersecurity researchers are flagging a spike in retaliatory hacktivist activity codenamed as ‘Epic Fury’ and ‘Roaring Lion’. The surge has primarily taken the form of distributed denial-of-service (DDoS) attacks, data leaks, and online disruption targeting both government and critical infrastructure organizations.
A new report describes how three main hacktivist groups, Keymous+, DieNet, and NoName057(16), have been responsible for nearly 70% of observed attack activity between February 28 and March 2, 2026. The first recorded attack during this period was launched by Hider Nex (aka Tunisian Maskers Cyber Force), a pro-Palestinian hacktivist collective that combines DDoS attacks with data breaches to support geopolitical messaging.
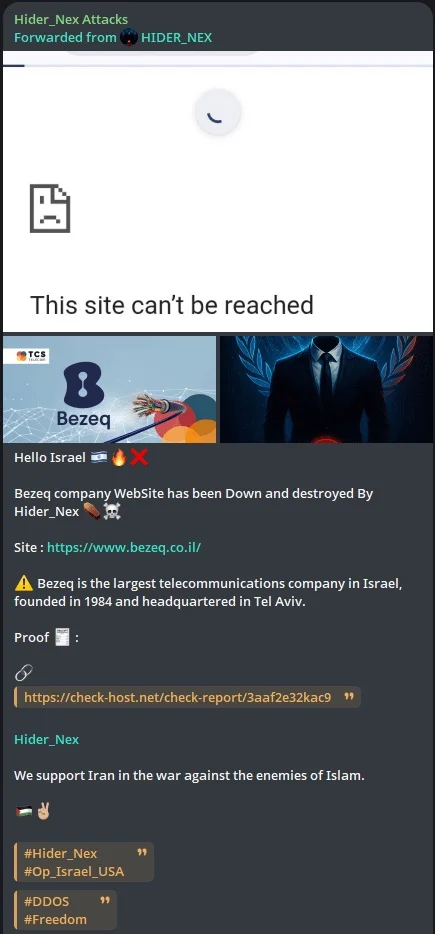
In total, researchers recorded 149 DDoS attacks targeting 110 organizations across 16 countries, carried out by 12 hacktivist groups. The majority of attacks focused on the Middle East, with 107 incidents targeting regional organizations. Government entities were the most affected sector, accounting for nearly 48% of the victims, followed by organizations in financial services and telecommunications.
Several other cyber threats have emerged alongside the hacktivist campaigns. Pro-Russian groups are claiming breaches of Israeli military networks, while threat actors have an active SMS phishing campaign distributing malware disguised as an Israeli civil defense alert app. Iranian state-linked actors associated with the Islamic Revolutionary Guard Corps (IRGC) have reportedly targeted regional energy and digital infrastructure, striking major oil refineries and data centers in the U.A.E.
Iranian-aligned cyber actors have historically blended espionage, disruption, and influence operations during geopolitical crises, suggesting the potential for broader targeting of government, infrastructure, financial, and technology sectors applicable on a global scale, too.
from SentinelOne https://ift.tt/wz6s7y2
via IFTTT
No comments:
Post a Comment