The Good | SentinelOne AI EDR Stops LiteLLM Supply Chain Attack in Real Time
This week, SentinelOne demonstrated how autonomous, AI-driven endpoint protection can detect and stop sophisticated supply chain attacks in real time, without human intervention. On the same day the attack was launched, Singularity Platform identified and blocked a trojanized version of LiteLLM, an increasingly popular proxy for LLM API calls, before it could execute across multiple customer environments. The compromise had occurred only hours earlier, yet the platform prevented execution instantly, without requiring analyst input, signatures, or manual triage.
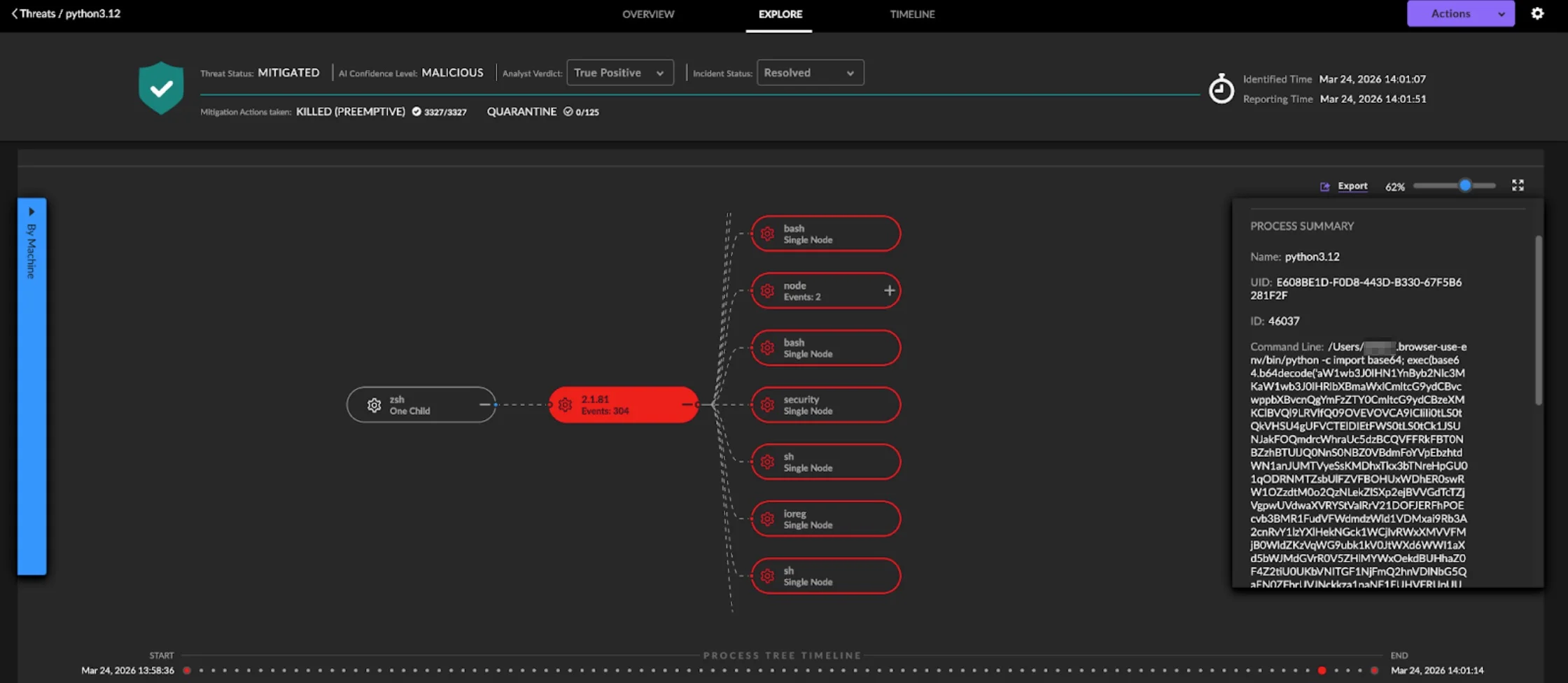
The attack itself followed a multi-stage, fast-moving, pattern that is designed to evade traditional detection and manual workflows. Originating from a compromised security tool, attackers obtained PyPi credentials to publish malicious LiteLLM versions that deployed a cross-platform payload. In one case, SentinelOne observed an AI coding assistant with unrestricted permissions unknowingly installing the infected package, highlighting a new and largely ungoverned attack surface.
Once triggered, the malware attempted to execute obfuscated Python code, deploy a data stealer, establish persistence, move laterally into Kubernetes clusters, and exfiltrate encrypted data. SentinelOne’s behavioral AI detected the malicious activity at runtime, specifically identifying suspicious execution patterns like base64-decoded payloads, and terminated the process chain in under 44 seconds while preserving full forensic visibility.
Critically, detection did not depend on knowing the compromised package. Instead, it relied on observing behavior across processes, allowing the platform to stop the attack regardless of how it entered the environment – whether via a developer, CI/CD pipeline, or autonomous agent.
This incident underscores a growing trend: AI-driven attacks are operating at speeds that outpace human response. Effective defense now requires autonomous, behavior-based systems capable of acting instantly, closing the gap between detection and compromise before damage can occur.
The Bad | Attackers Compromise Axios to Deliver Cross-Platform RAT via Compromised npm
For JavaScript HTTP client Axios, a major supply chain attack compromised its systems after malicious versions of an npm package introduced a hidden dependency that deploys a cross-platform remote access trojan (RAT). Specifically, Axios versions 1.14.1 and 0.30.4 were found to include a rogue package called “plain-crypto-js@4.2.1,” inserted using stolen npm credentials that belonged to a core maintainer. This allowed attackers to bypass normal CI/CD safeguards and publish poisoned releases directly to npm.
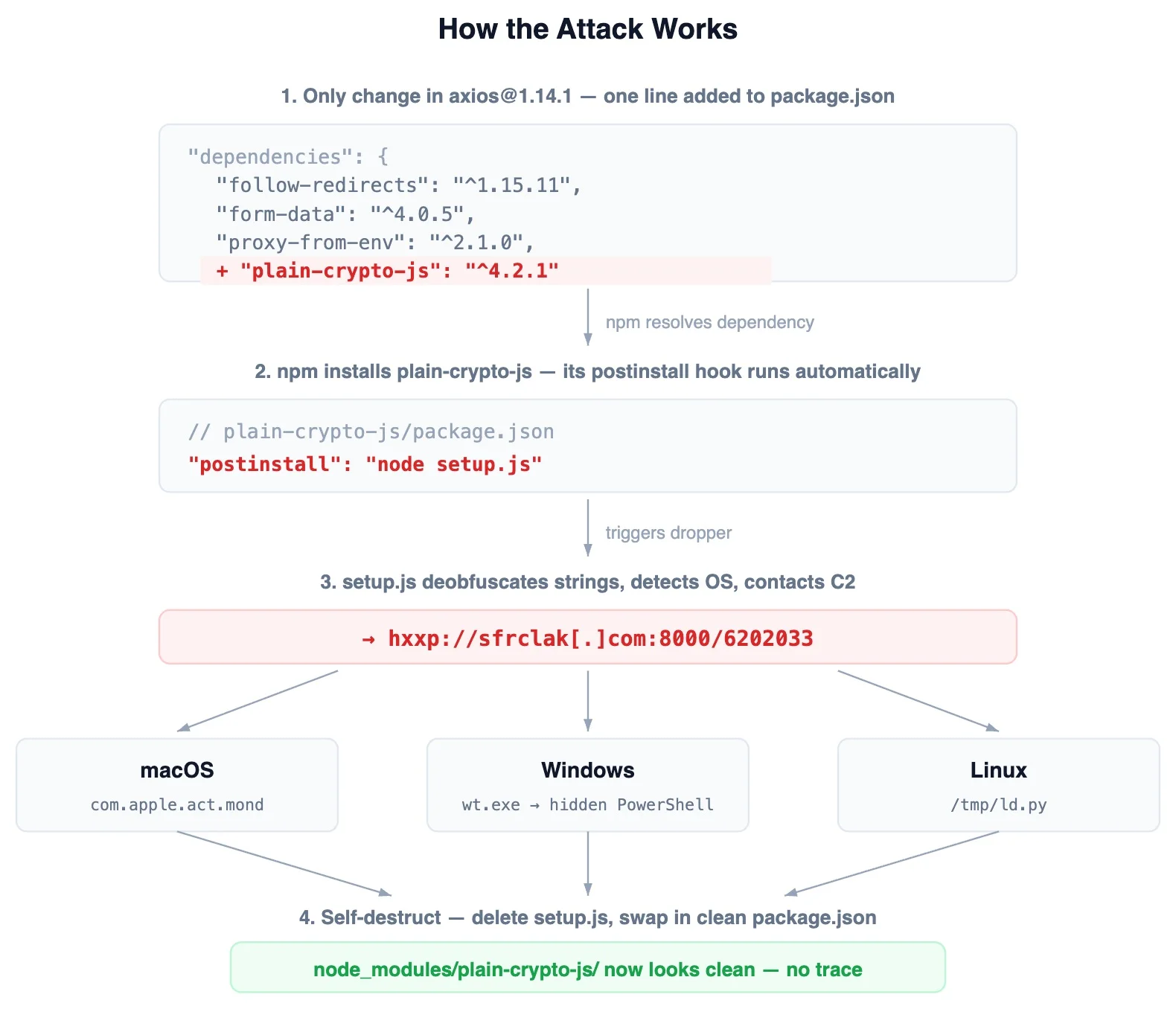
The malicious dependency exists solely to execute a post-install script that downloads and runs platform-specific malware on macOS, Windows, and Linux systems. Once executed, the malware connects to a command and control (C2) server, retrieves a second-stage payload, and then deletes itself while restoring clean-looking package files to evade detection. Notably, no malicious code exists within Axios itself, making the attack harder to detect through traditional code review.
The operation was highly coordinated, with staged payloads prepared in advance and both affected Axios branches compromised within minutes. Each platform-specific variant – C++ for macOS, PowerShell for Windows, and Python for Linux – shares the same functionality, enabling system reconnaissance, command execution, and data exfiltration. While macOS and Linux variants lack persistence, the Windows version establishes ongoing access via registry modifications.
Researchers believe the attacker leveraged a long-lived npm access token to gain control of the maintainer account. There are also indications linking the malware to previously observed tooling associated with a North Korean threat group known as UNC1069.
Users are strongly advised to downgrade Axios immediately to versions 1.14.0 or 0.30.3, remove the malicious dependency, check for indicators of compromise, and rotate all credentials if exposure is suspected.
The Ugly | High-Severity Chrome Zero-Day in Dawn Component Allows Remote Code Execution
Google has issued security updates for its Chrome browser to address 21 vulnerabilities, including a high-severity zero-day flaw, tracked as CVE-2026-5281, that is actively being exploited in the wild. The vulnerability stems from a use-after-free (UAF) bug in Dawn, an open-source implementation of the WebGPU standard used by Chromium. If successfully exploited, it allows attackers who have already compromised the browser’s renderer process to execute arbitrary code via a specially crafted HTML page.
While Google has confirmed active exploitation, it has withheld technical details and attribution to limit further abuse until more users apply the patch. This zero-day is the latest in a series of actively-exploited Chrome flaws addressed in 2026 so far, bringing the total to four for this year alone. Previous issues included vulnerabilities in Chrome’s CSS component, Skia graphics library, and V8 JavaScript engine.
The Dawn flaw could lead to browser crashes, memory corruption, or other erratic behavior, underscoring the risks posed by modern browser attack surfaces. To date, Google has released fixes in Chrome version 146.0.7680.177/178 for Windows and macOS, and 146.0.7680.177 for Linux, now available through the Stable Desktop channel.
To protect against the flaw, Users can update Chrome immediately by navigating to the browser’s settings and relaunching after installation. Other Chromium-based browsers, including Microsoft Edge, Brave, Opera, and Vivaldi, are also expected to roll out patches and should be updated promptly. CISA has added the flow to its KEV catalog and mandated that FCEB agencies apply the patch by April 15, 2026 to prevent their networks from attack. This latest incident highlights the ongoing targeting of web browsers by threat actors and reinforces the importance of timely patching to mitigate exploitation risks.
from SentinelOne https://ift.tt/LSRce0Y
via IFTTT

No comments:
Post a Comment