
Speed and age shouldn’t be allowed to pair up, but that is the theme of the Talos 2025 Year in Review vulnerability findings.

The year was characterized by an unending beat-down on infrastructure that relied on older enmeshed dependencies (e.g., Log4j and PHPUnit), while React2Shell rocketed to the highest percentage of attacks for the entire year within the last three weeks of 2025. Agentic AI's capacity for building and deploying new proofs-of-concepts and exploit kits lowered attacker time-to-exploit, and the landscape shifted for defenders.
“The speed at which these CVEs climbed into the top tier reflects a larger systemic challenge: Newly disclosed vulnerabilities in widely deployed software can generate significant, organization-wide impact long before typical patch cycles catch up, leaving defenders with small reaction windows and escalating consequences for even short-lived exposure.” – 2025 Talos Year in Review
Top-targeted infrastructure
Outdated infrastructure continues to expand the attack surface. Components like PHPUnit, ColdFusion, and Log4j are often embedded within applications, tightly coupled to legacy applications. Technologies age quickly, and companies are under pressure to adopt first, ask questions later. Low-use systems in a network can fossilize, unnoticed and unpatched. Others become mainstays that often cannot be swapped out or even patched without destabilizing an organization.
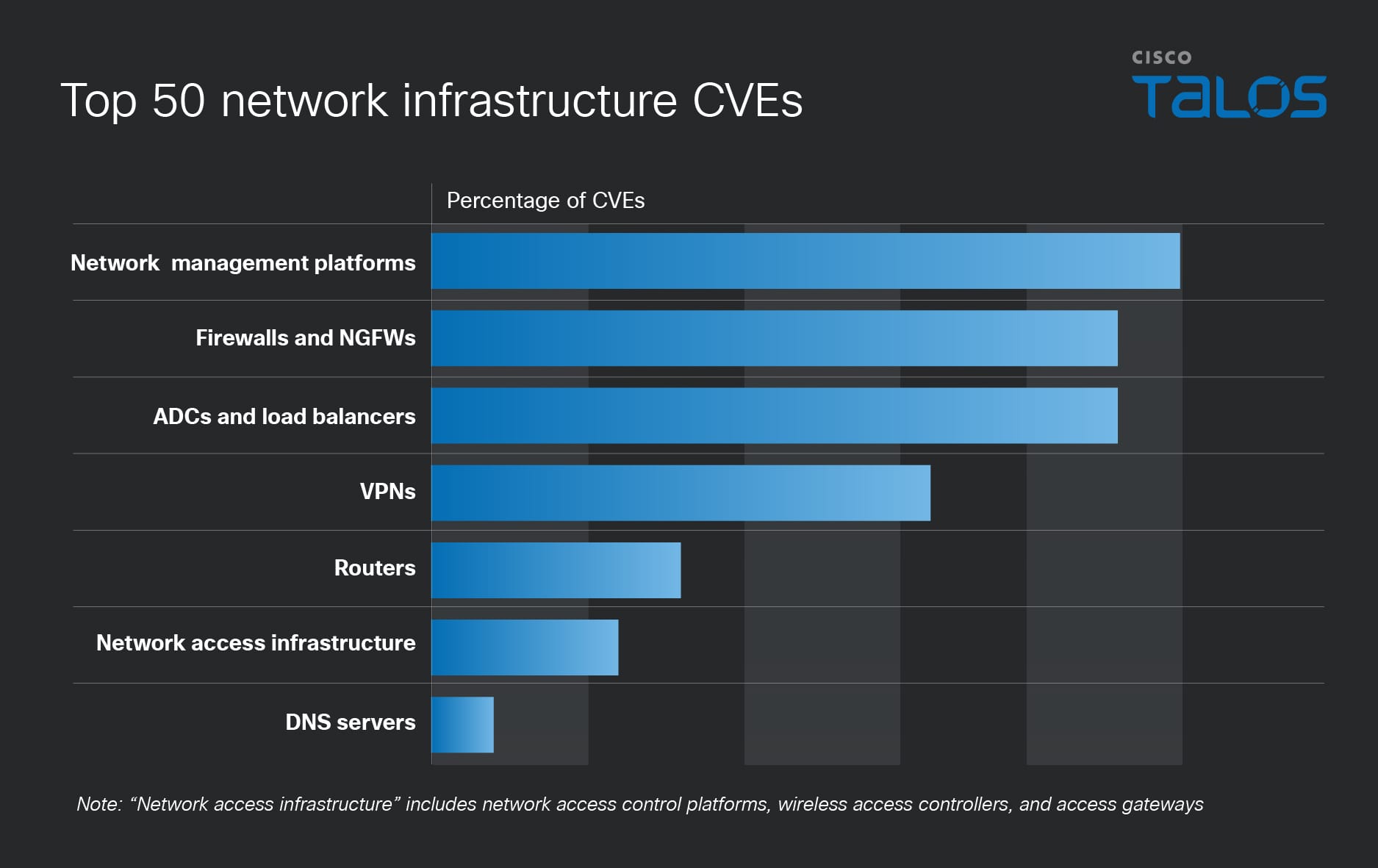
Attackers prioritized software and firmware inside network appliances, identity-adjacent systems, and widely deployed open-source components:
- Remote code execution (RCE) flaws, which enable access without requiring user interaction, avoiding a need for social engineering
- Legacy systems and widely used components
- Perimeter devices, especially without endpoint detection and response (EDR)
The theme was identity, identity, identity. Controlling identity meant controlling access, so attackers focused on components that authenticate users, enforce access decisions, and broker trust between systems. A small number of vulnerabilities targeting these vectors drove outsized risk. This can invalidate multi-factor authentication (MFA) checks and bypass segmentation.
Defender recommendations
Attacker prioritization is now guided less by vulnerability age or maturity and more by exposure, exploitability, and proximity to trust, reshaping how organizations must think about risk in modern environments.
Attackers exploit patching gaps and policy weaknesses in vendor lifecycles. Organizations should evaluate their identity-centric network components and management platforms and prioritize patching of network devices accordingly.
For a more in-depth analysis of these trends, as well as how company size impacted CVE targeting trends, why the management plane matters, and the shortening window defenders have for putting defenses in place, see the 2025 Year in Review report.
from Cisco Talos Blog https://ift.tt/cP8guiV
via IFTTT
No comments:
Post a Comment